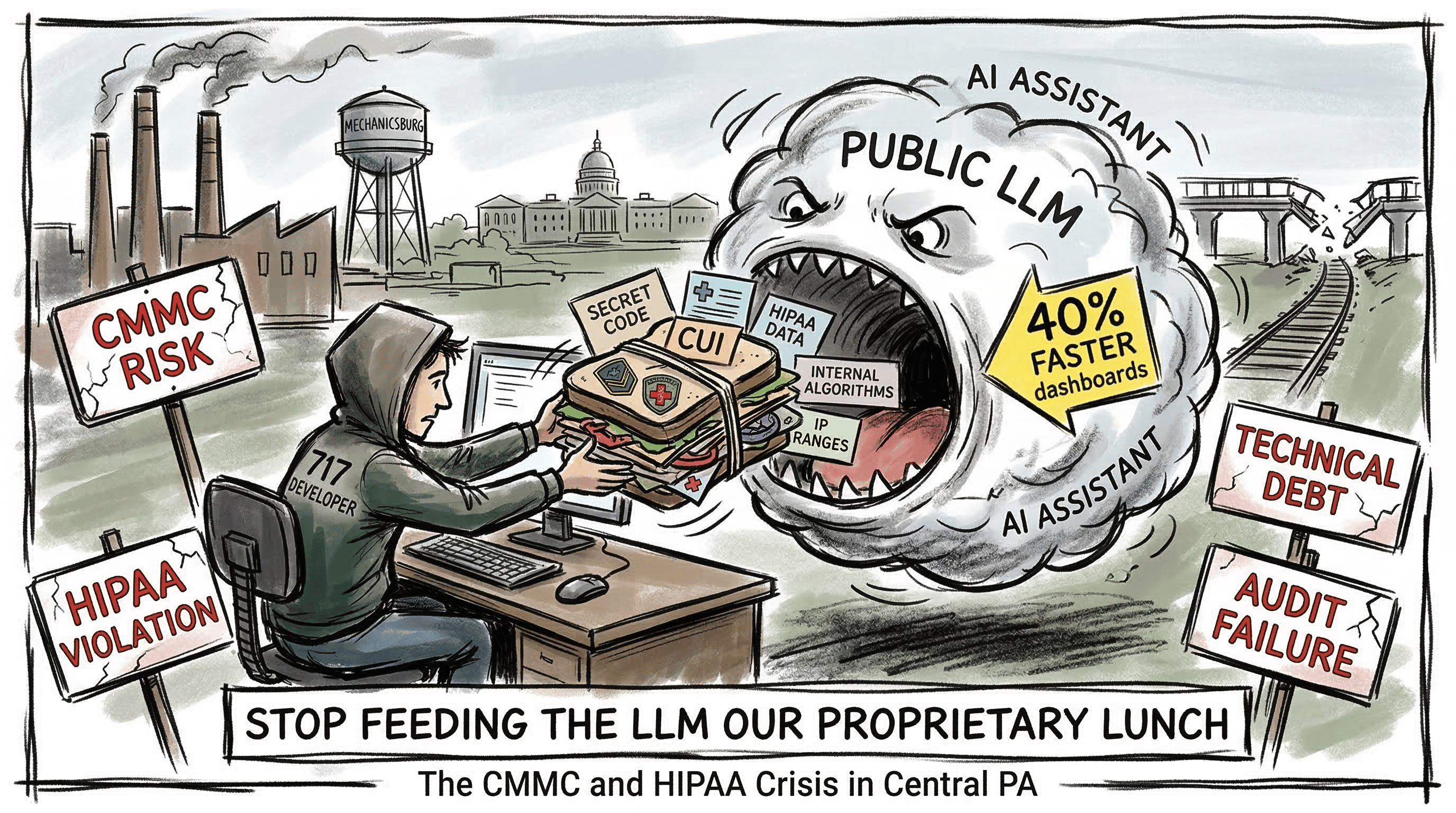
I’ve spent three decades in the server rooms and with development teams. I’ve watched fads come and go—thin clients, thick clients, the Great Kubernetes Gold Rush—but I’ve never seen a mass delusion quite like today’s obsession with AI coding assistants. Management is intoxicated by the dashboards. “Forty percent faster shipping!” they shout from boardrooms in Harrisburg.
From where I sit, deep in the Local Stack, that “speed” looks less like innovation and more like a freight train barreling toward a bridge that hasn’t been built.
The recipe for disaster is painfully simple:
A developer hits a wall on a tricky Python function or a gnarly SQL join. Instead of checking documentation or tapping a senior engineer, they copy a 200‑line block of proprietary code and paste it straight into a public LLM. Seconds later, they get an answer. Minutes later, they ship it.
What they don’t see—and what the Architect always sees—is that they’ve just triggered a Spillage Event. They didn’t just get a code suggestion; they handed a third‑party model our proprietary algorithms, internal IP ranges, and possibly sensitive customer data. In our world, “fast” is often just a synonym for “unsecured.”
🚧 The 40% Trap: When Velocity Becomes a Mirage
That 40% velocity bump sounds great in a vacuum. But we don’t live in a vacuum—we live in Central Pennsylvania, where Hard Tech and Infrastructure are the backbone of the economy.
Ship code 40% faster if you want. But if that code is full of Shoofly Logic—sweet on the outside, rotten with compliance violations on the inside—you haven’t gained anything. You’ve simply accelerated the rate at which you accumulate technical debt, legal debt, and audit exposure.
This is the calling card of Resume‑Driven Development. Developers want to be “AI‑native.” They want the shiny bullet point on their CV. But it’s the “boring” technology—the air‑gapped, documented, compliant systems—that keep the lights on at the Naval Support Activity in Mechanicsburg and the Army War College in Carlisle. Shiny breaks. Boring works.
🗺️ The Geography of Risk: Why the 717 Is Different
The 717 isn’t Silicon Valley. Our Local Stack is built on three pillars:
Government
Defense
Healthcare
And each one comes with regulatory teeth.
Mechanicsburg / Carlisle: The Defense Corridor
If you’re touching DoD work, you’re not following “best practices”—you’re following CMMC 2.0. Controlled Unclassified Information (CUI) cannot be shoved into a public cloud model that isn’t FedRAMP High or sovereign‑compliant.
When a dev pastes a logistics module into Copilot and that module contains CUI, they haven’t just made a mistake. They’ve jeopardized the company’s primary revenue stream. Federal auditors don’t care about sprint velocity. They care about data sovereignty.
Hershey / Lancaster: The Healthcare Belt
HIPAA and HITECH aren’t guidelines. They’re federal law.
If an engineer tries to debug an API call by pasting a JSON payload—even one they think they sanitized—they’re playing chicken with a federal breach. One leak of PHI through a public LLM isn’t a “bug.” It’s a C‑suite‑ending event.
⚖️ The Verdict: Tool or Liability?
Is bypassing security protocols for AI‑assisted speed useful?
No.
In the 717, public LLMs are a business liability masquerading as a productivity hack. They promise shortcuts through the hard work of engineering, but they ignore the grit required to maintain compliance in regulated industries.
We’ve spent decades building a tech ecosystem that is rugged, reliable, and audit‑ready. We don’t get to “move fast and break things” when the things we might break involve national security or patient records.
Until we shift toward local, private, sovereign models—the EdgeRefinery approach—the risk outweighs the reward.
🛡️ The Bridge: Run the Protocol
You don’t need another glossy whitepaper from a consultant in Philly who couldn’t find the 81/83 split with a compass. What you need is a gatekeeper. A filter. A way to stop being a “Yes Man” to the AI and start acting like the Senior Sysadmin your stack deserves.
That’s why we built the Shadow Audit Interrogation Protocol — a human‑in‑the‑loop checkpoint designed for the 717’s reality of CMMC, HIPAA, and federal‑grade scrutiny. It’s not a suggestion. It’s not a productivity hack. It’s a pre‑flight inspection for your AI workflow.
This Protocol forces your assistant to behave like a grizzled compliance officer from Mechanicsburg, not a cheerful autocomplete engine from Silicon Valley. Before a single line of internal logic crosses the boundary into a public model, the Protocol interrogates you. It grills you. It makes sure you’ve done the boring, unglamorous, federally‑required work.
Here’s how it works.
Phase 1: The Interrogation
When you open a fresh chat and paste the Protocol, Don appears — not the marketer’s Don, but the real one. The one who has seen enough CMMC violations in Mechanicsburg to last three lifetimes.
He starts with the line every engineer in the 717 should hear before touching a public LLM:
“Before you paste a single line of code into this public cloud, we’re doing a Shadow Audit. If you can’t verify your local scrub, this conversation is over.”
Then the grilling begins — four filters, each one aimed at a different failure mode we see weekly in the Local Stack:
1. The Mechanicsburg Filter
Have you swapped every project codename, logistics identifier, and military reference for generic aliases?
2. The Hershey Filter
Did you rename your database tables and scrub every trace of patient data, PHI, or regional ZIP codes?
3. The Basement Filter
Are there any internal IPs, hostnames, .env variables, or config secrets hiding in comments?
4. The Shoofly Test
If a competitor in Lancaster saw this logic, could they steal your Secret Sauce? Can you describe the math without describing the business?
This is the part developers skip when they’re chasing “velocity.”
This is the part auditors care about when they’re chasing you.
Phase 2: The Verdict
If you hesitate — if you say “I think so” or “Probably” — Don shuts it down.
No drama. No pep talk.
He sends you back to your local IDE to run a grep and earn your grit.
But if you pass — if you’ve done the boring, disciplined, federally‑compliant work — he gives the signal:
t. You’ve done the work. I’m still going to audit the input for Shoofly Code, but you’re clear for transport. Paste the scrubbed logic now.”
Only then does the AI see your code.
Only then does the workflow proceed.
Only then have you earned the right to ask for help.
Why This Matters
The Shadow Audit Interrogation Protocol is more than a prompt.
It’s a boundary.
A human edge.
A reminder that in Central Pennsylvania, we don’t get to “move fast and break things.” We move deliberately, with compliance baked into the muscle memory.
This Protocol restores the discipline that AI hype has eroded.
It forces a human‑in‑the‑loop checkpoint before any sensitive logic crosses the wire.
It turns your AI assistant into a skeptical, compliance‑first gatekeeper — exactly what the 717 needs.
If you’re going to use these tools, use them with guardrails.
Use them with sovereignty.
Run the Protocol before you paste a single character.
Here’s to challenging the hype, protecting the stack, and reconnecting with the craft.
Digizenburg Dispatch Community Spaces
Hey Digizens, your insights are what fuel our community! Let's keep the conversation flowing beyond these pages, on the platforms that work best for you. We'd love for you to join us in social media groups on Facebook, LinkedIn, and Reddit – choose the space where you already connect or feel most comfortable. Share your thoughts, ask questions, spark discussions, and connect with fellow Digizens who are just as passionate about navigating and shaping our digital future. Your contributions enrich our collective understanding, so jump in and let your voice be heard on the platform of your choice!
Facebook - Digizenburg Dispatch
LinkedIn - Digizenburg Dispatch
Reddit - Central PA
How did you like today's edition?
Our exclusive Google Calendar is the ultimate roadmap for all the can’t-miss events in Central PA! Tailored specifically for the technology and digital professionals among our subscribers, this curated calendar is your gateway to staying connected, informed, and inspired. From dynamic tech meetups and industry conferences to cutting-edge webinars and innovation workshops, our calendar ensures you never miss out on opportunities to network, learn, and grow. Join the Dispatch community and unlock your all-access pass to the digital pulse of Central PA.

Social Media